1
What Problem Am I Solving?
Throughout my process of studying for the OSCP, I found that there were too few labs with multiple machines chained together that were publicly available.
The ones that were available seemed to have hit the same subjects repeatedly. I needed a comprehensive
lab environment that could test various attack surfaces and network configurations.
2
Why Does That Problem Matter?
This problem had to be solved for the purpose of preparation. I felt the need of having to go through
every possible attack surface, leave no stone unturned, and learn more about developing enterprise
networks and securing them. A robust lab environment enables hands-on learning with real-world scenarios
that can't be replicated through reading alone.
3
What Did I Do?
I virtualized an "OSCP-Style" active directory lab environment. This consisted of:
- Domain Controller (Windows Server)
- Windows Server 2022 (member server)
- Windows 11 machine (client workstation)
- Kali Linux (attacker machine)
The environment was designed to simulate a small enterprise network with isolated network segments
and controlled connectivity.
4
How Did I Do It?
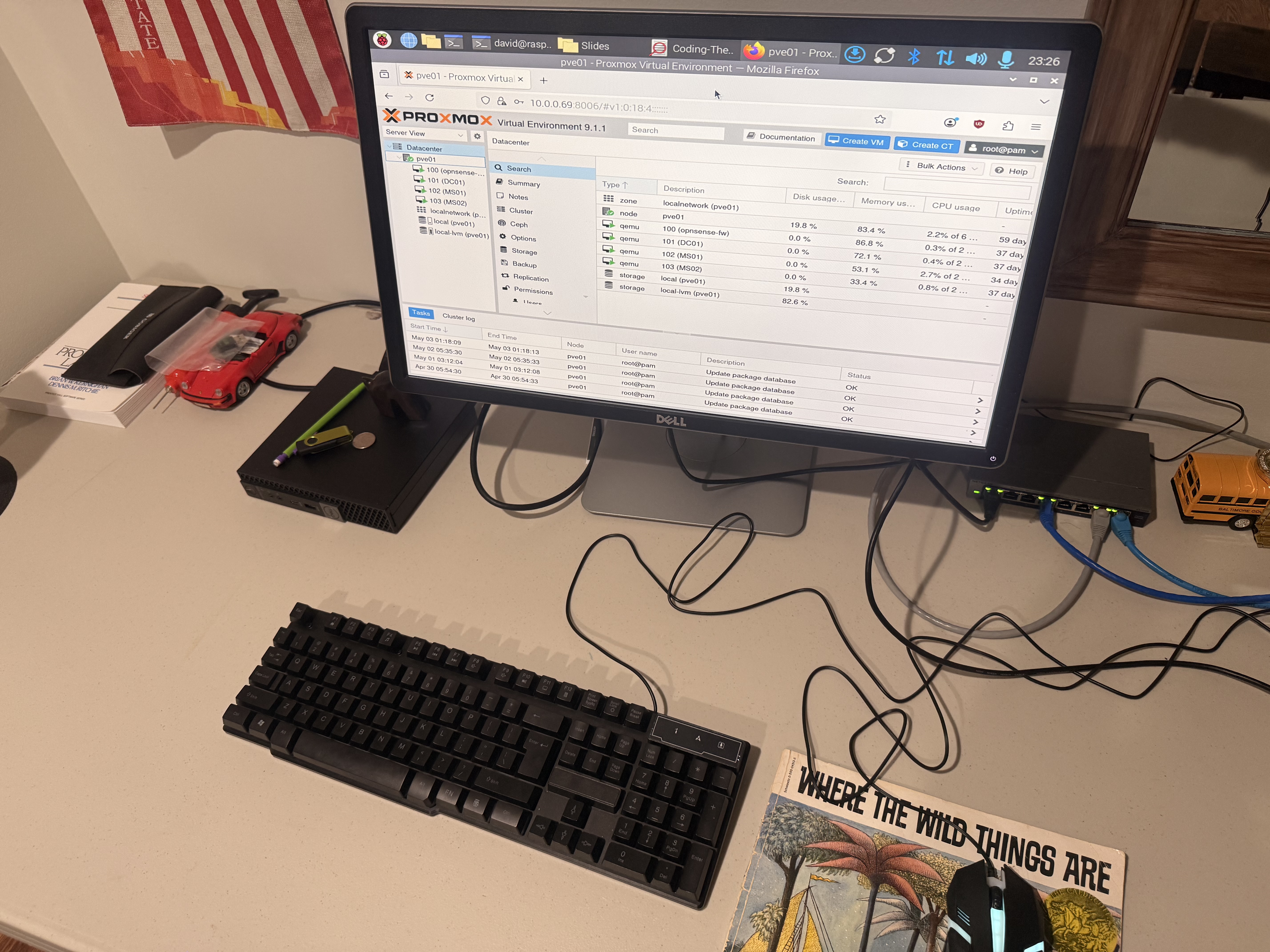
I used a combination of virtualization and networking tools to create the lab:
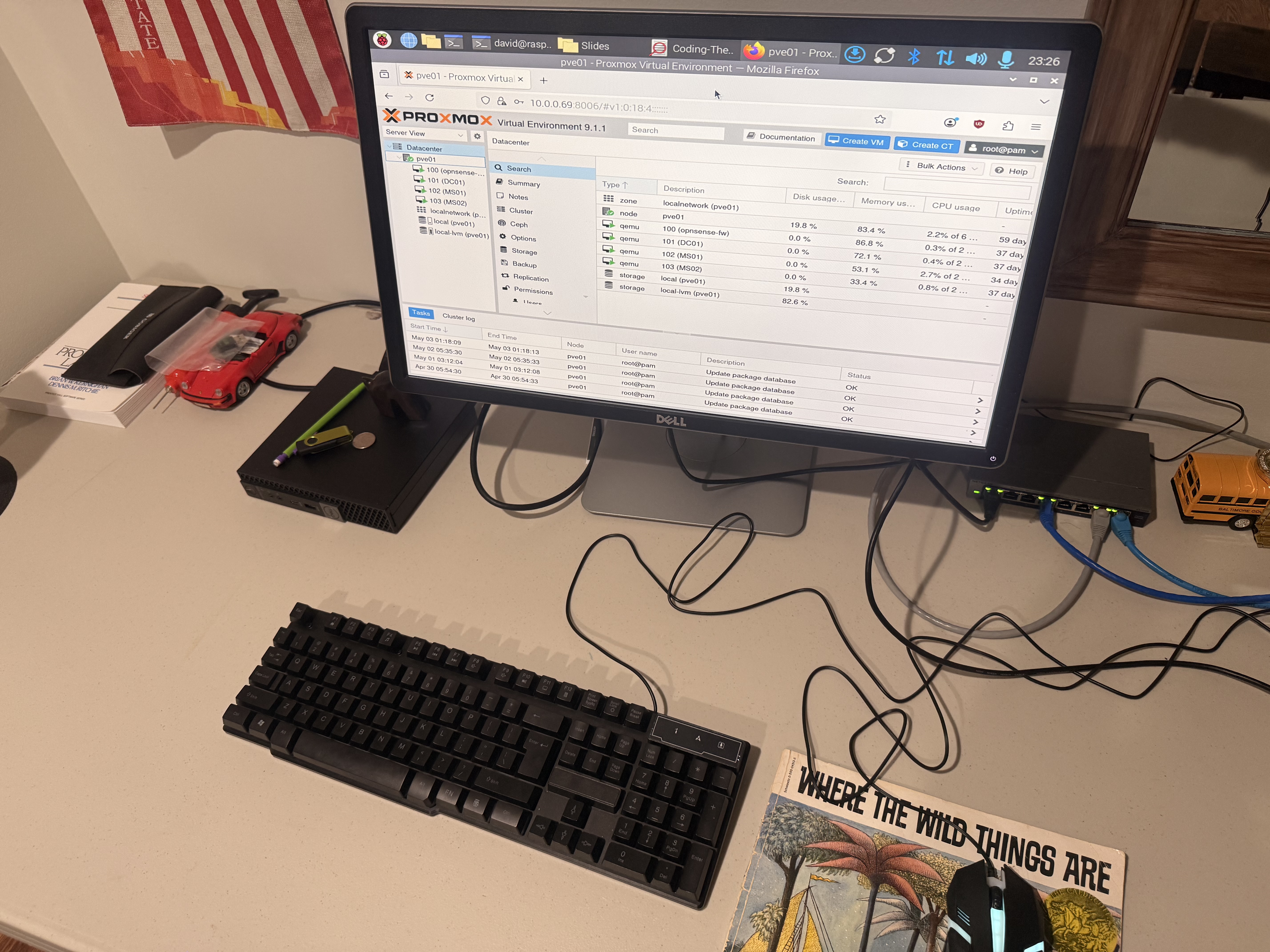
Proxmox
OPNSense
Kali Linux
Active Directory
Windows Server
- Virtualization: Used Proxmox for VM management and resource allocation
- Network Management: Configured OPNSense for routing and firewall rules
- Offensive Tools: Deployed Kali Linux for executing offensive security tools
- Directory Services: Set up Active Directory for domain management and group policies
5
What Challenges Did I Hit?
🔴 Routing Issues: Network traffic wasn't routing correctly between VLANs and segments
🔴 Connectivity Restrictions: Internal computers were not allowed to communicate with external sources,
requiring careful firewall rule design
🔴 OSCP-like environment: Ensuring the lab architecture met all OSCP exam requirements and restrictions
🔴 Resource Constraints: Managing CPU, memory, and disk allocation across multiple VMs
6
How Did I Solve These Challenges?
✅ Persistence: Systematically tested each routing rule and validated traffic flow through packet capture
✅ Firewall Design: Created explicit ingress/egress rules using OPNSense to enforce network segmentation
✅ Documentation: Maintained detailed network diagrams and configuration notes for reproducibility
✅ Incremental Testing: Built and tested the lab environment piece by piece rather than all at once
7
Results
Working lab environment capable of emulating any attack surfaces I want.
I can go down an arbitrary list, take good notes, and be well prepared for the exam.
Key Achievements:
- Successfully isolated lab network from external internet
- Implemented multiple attack scenarios and privilege escalation paths
- Created repeatable lab configurations for future use
- Achieved OSCP-compliant environment setup
- Comprehensive hands-on experience with enterprise network security